
Multi-factor authentication (or MFA) is more or less exactly what it sounds like. To access an application, you first need to pass two or more phases of verification. MFA is an extra step to ensure that you are who you say you are.
For businesses, Multi-factor authentication is a security must-have. Gone are the days when a username and password were enough. Users can access Cloud applications from anywhere, which means hackers can too. We need extra measures to block third party hackers and other malware. MFA is important to ensure protection for users and organisations alike.
What is Multi-Factor Authentication?
Multi-Factor Authentication is a method which requires that the person should seek data for the verification of identity in two or more ways. Watch below for an in-depth explanation:
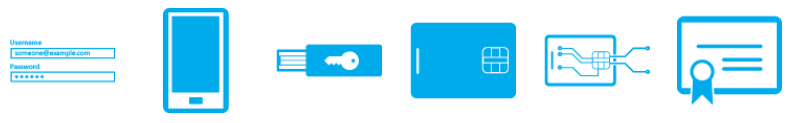
The verifications are usually a combination of two of the below:
- Validation of your password
- Utilising your mobile phone via text or Authenticator App
- Biometrics such as fingerprint, iris or face recognition
The idea of MFA is to keep multiple layers of protection in a way that so that it should be difficult to gain access to your account.
Multi-Factor Authentication (MFA) gives you the power because defeating a biometric challenge or an extra layer of device security is a challenging thing to do!
Why use Multi-Factor Authentication?
Quite simply, Multi-factor authentication has evolved as the single most effective control to insulate an organisation against remote attacks and when implemented correctly, can prevent most threat actors from easily gaining an initial foothold into your organisation, even if credentials become compromised.
Different types of MFA
OTPs (One time passwords)
Personal security questions
Voice and facial recognition
Fingerprints and other biometrics
Location-based MFA
A note on Google Authenticator, Authy, and other MFA applications
What’s the difference between MFA and 2FA?
What are the benefits of Multi-Factor Authentication?
- Simplifies the login process as you can gain access to required applications and data without entering your extra credentials every time making it a smoother process for the end user.
- Increased Flexibility and Productivity by removing the burden of entering long, time consuming passwords.
- Strengthen overall security as everything required by the system is not available to the people wanting to steal your data and gain access to your system.
- Take a step towards compliance that will support the protection of sensitive data like your financial, personal or business information.
Multi-Factor Authentication with Microbyte
To summarise, with the increase of cyber-attacks on organisations, password strength cannot be relied on as the only layer of protection for an organisation to preventing threat actors from gaining unauthorised access. Although not bullet-proof, multi-factor authentication is a proven way to lessen the likelihood of a data breach via a compromised password. Want to learn more about how Microbyte can help your organisation prevent an attack through multi-factor authentication? Contact us today!





